企业安全-学习Kubernetes笔记——暴露站点服务(Ingress)
推荐 原创这是我踩坑最多的一个地方 QAQ
Ingress 是什么?
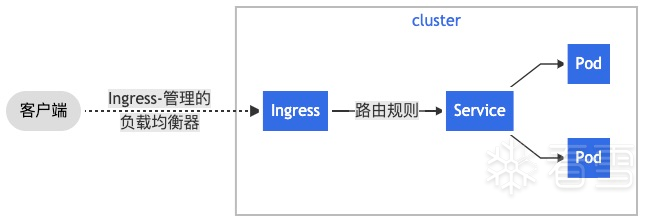
Kubernetes 暴露服务的方式目前只有三种:LoadBlancer Service、NodePort Service、Ingress。
可以将 Ingress 配置为服务提供外部可访问的 URL、负载均衡流量、终止 SSL/TLS,以及提供基于名称的虚拟主机等能力。 通常负责通过负载均衡器来实现 Ingress,尽管它也可以配置边缘路由器或其他前端来帮助处理流量。
Ingress 不会公开任意端口或协议。将 HTTP 和 HTTPS 以外的服务公开到 Internet 时,通常使用 Service.Type=NodePort 或 Service.Type=LoadBalancer 类型的服务。
下面是一个将所有流量都发送到同一 Service 的简单 Ingress 示例:
使用Ingress的好处:
- 端口管理。减少不必要端口暴露,便于管理。
所有的请求,通过Ingress对应的IP:PORT进入,过滤/转发/负载均衡到相应的service/pod。 NodePort会在每个node上暴露对应的port,不便管理。
环境准备
要用Ingress,必须安装在K8S中安装Ingress控制器
Ingress 控制器有非常非常多,这里采用的Ingress+Nginx,采用其他控制器可查阅
Ingress控制器的部署方式也有很多,可查阅
接下来踩坑最多的地方来了
有条件的话,推荐执行官方YAML文件
|
1
|
kubectl
apply
-
f https:
/
/
raw.githubusercontent.com
/
kubernetes
/
ingress
-
nginx
/
controller
-
v1.
5.1
/
deploy
/
static
/
provider
/
cloud
/
deploy.yaml
|
已修改版,可直接使用
|
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
85
86
87
88
89
90
91
92
93
94
95
96
97
98
99
100
101
102
103
104
105
106
107
108
109
110
111
112
113
114
115
116
117
118
119
120
121
122
123
124
125
126
127
128
129
130
131
132
133
134
135
136
137
138
139
140
141
142
143
144
145
146
147
148
149
150
151
152
153
154
155
156
157
158
159
160
161
162
163
164
165
166
167
168
169
170
171
172
173
174
175
176
177
178
179
180
181
182
183
184
185
186
187
188
189
190
191
192
193
194
195
196
197
198
199
200
201
202
203
204
205
206
207
208
209
210
211
212
213
214
215
216
217
218
219
220
221
222
223
224
225
226
227
228
229
230
231
232
233
234
235
236
237
238
239
240
241
242
243
244
245
246
247
248
249
250
251
252
253
254
255
256
257
258
259
260
261
262
263
264
265
266
267
268
269
270
271
272
273
274
275
276
277
278
279
280
281
282
283
284
285
286
287
288
289
290
291
292
293
294
295
296
297
298
299
300
301
302
303
304
305
306
307
308
309
310
311
312
313
314
315
316
317
318
319
320
321
322
323
324
325
326
327
328
329
330
331
332
333
334
335
336
337
338
339
340
341
342
343
344
345
346
347
348
349
350
351
352
353
354
355
356
357
358
359
360
361
362
363
364
365
366
367
368
369
370
371
372
373
374
375
376
377
378
379
380
381
382
383
384
385
386
387
388
389
390
391
392
393
394
395
396
397
398
399
400
401
402
403
404
405
406
407
408
409
410
411
412
413
414
415
416
417
418
419
420
421
422
423
424
425
426
427
428
429
430
431
432
433
434
435
436
437
438
439
440
441
442
443
444
445
446
447
448
449
450
451
452
453
454
455
456
457
458
459
460
461
462
463
464
465
466
467
468
469
470
471
472
473
474
475
476
477
478
479
480
481
482
483
484
485
486
487
488
489
490
491
492
493
494
495
496
497
498
499
500
501
502
503
504
505
506
507
508
509
510
511
512
513
514
515
516
517
518
519
520
521
522
523
524
525
526
527
528
529
530
531
532
533
534
535
536
537
538
539
540
541
542
543
544
545
546
547
548
549
550
551
552
553
554
555
556
557
558
559
560
561
562
563
564
565
566
567
568
569
570
571
572
573
574
575
576
577
578
579
580
581
582
583
584
585
586
587
588
589
590
591
592
593
594
595
596
597
598
599
600
601
602
603
604
605
606
607
608
609
610
611
612
613
614
615
616
617
618
619
620
621
622
623
624
625
626
627
628
629
630
631
632
633
634
635
636
637
638
639
640
641
642
643
644
645
646
647
648
649
650
651
652
653
654
655
656
657
658
659
660
661
662
663
664
665
666
667
668
669
670
671
672
673
|
# Source: ingress-nginx/templates/controller-serviceaccount.yaml
apiVersion: v1
kind: ServiceAccount
metadata:
labels:
helm.sh
/
chart: ingress
-
nginx
-
4.0
.
1
app.kubernetes.io
/
name: ingress
-
nginx
app.kubernetes.io
/
instance: ingress
-
nginx
app.kubernetes.io
/
version:
1.0
.
0
app.kubernetes.io
/
managed
-
by: Helm
app.kubernetes.io
/
component: controller
name: ingress
-
nginx
namespace: ingress
-
nginx
automountServiceAccountToken: true
-
-
-
# Source: ingress-nginx/templates/controller-configmap.yaml
apiVersion: v1
kind: ConfigMap
metadata:
labels:
helm.sh
/
chart: ingress
-
nginx
-
4.0
.
1
app.kubernetes.io
/
name: ingress
-
nginx
app.kubernetes.io
/
instance: ingress
-
nginx
app.kubernetes.io
/
version:
1.0
.
0
app.kubernetes.io
/
managed
-
by: Helm
app.kubernetes.io
/
component: controller
name: ingress
-
nginx
-
controller
namespace: ingress
-
nginx
data:
-
-
-
# Source: ingress-nginx/templates/clusterrole.yaml
apiVersion: rbac.authorization.k8s.io
/
v1
kind: ClusterRole
metadata:
labels:
helm.sh
/
chart: ingress
-
nginx
-
4.0
.
1
app.kubernetes.io
/
name: ingress
-
nginx
app.kubernetes.io
/
instance: ingress
-
nginx
app.kubernetes.io
/
version:
1.0
.
0
app.kubernetes.io
/
managed
-
by: Helm
name: ingress
-
nginx
rules:
-
apiGroups:
-
''
resources:
-
configmaps
-
endpoints
-
nodes
-
pods
-
secrets
verbs:
-
list
-
watch
-
apiGroups:
-
''
resources:
-
nodes
verbs:
-
get
-
apiGroups:
-
''
resources:
-
services
verbs:
-
get
-
list
-
watch
-
apiGroups:
-
networking.k8s.io
resources:
-
ingresses
verbs:
-
get
-
list
-
watch
-
apiGroups:
-
''
resources:
-
events
verbs:
-
create
-
patch
-
apiGroups:
-
networking.k8s.io
resources:
-
ingresses
/
status
verbs:
-
update
-
apiGroups:
-
networking.k8s.io
resources:
-
ingressclasses
verbs:
-
get
-
list
-
watch
-
-
-
# Source: ingress-nginx/templates/clusterrolebinding.yaml
apiVersion: rbac.authorization.k8s.io
/
v1
kind: ClusterRoleBinding
metadata:
labels:
helm.sh
/
chart: ingress
-
nginx
-
4.0
.
1
app.kubernetes.io
/
name: ingress
-
nginx
app.kubernetes.io
/
instance: ingress
-
nginx
app.kubernetes.io
/
version:
1.0
.
0
app.kubernetes.io
/
managed
-
by: Helm
name: ingress
-
nginx
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: ClusterRole
name: ingress
-
nginx
subjects:
-
kind: ServiceAccount
name: ingress
-
nginx
namespace: ingress
-
nginx
-
-
-
# Source: ingress-nginx/templates/controller-role.yaml
apiVersion: rbac.authorization.k8s.io
/
v1
kind: Role
metadata:
labels:
helm.sh
/
chart: ingress
-
nginx
-
4.0
.
1
app.kubernetes.io
/
name: ingress
-
nginx
app.kubernetes.io
/
instance: ingress
-
nginx
app.kubernetes.io
/
version:
1.0
.
0
app.kubernetes.io
/
managed
-
by: Helm
app.kubernetes.io
/
component: controller
name: ingress
-
nginx
namespace: ingress
-
nginx
rules:
-
apiGroups:
-
''
resources:
-
namespaces
verbs:
-
get
-
apiGroups:
-
''
resources:
-
configmaps
-
pods
-
secrets
-
endpoints
verbs:
-
get
-
list
-
watch
-
apiGroups:
-
''
resources:
-
services
verbs:
-
get
-
list
-
watch
-
apiGroups:
-
networking.k8s.io
resources:
-
ingresses
verbs:
-
get
-
list
-
watch
-
apiGroups:
-
networking.k8s.io
resources:
-
ingresses
/
status
verbs:
-
update
-
apiGroups:
-
networking.k8s.io
resources:
-
ingressclasses
verbs:
-
get
-
list
-
watch
-
apiGroups:
-
''
resources:
-
configmaps
resourceNames:
-
ingress
-
controller
-
leader
verbs:
-
get
-
update
-
apiGroups:
-
''
resources:
-
configmaps
verbs:
-
create
-
apiGroups:
-
''
resources:
-
events
verbs:
-
create
-
patch
-
-
-
# Source: ingress-nginx/templates/controller-rolebinding.yaml
apiVersion: rbac.authorization.k8s.io
/
v1
kind: RoleBinding
metadata:
labels:
helm.sh
/
chart: ingress
-
nginx
-
4.0
.
1
app.kubernetes.io
/
name: ingress
-
nginx
app.kubernetes.io
/
instance: ingress
-
nginx
app.kubernetes.io
/
version:
1.0
.
0
app.kubernetes.io
/
managed
-
by: Helm
app.kubernetes.io
/
component: controller
name: ingress
-
nginx
namespace: ingress
-
nginx
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: Role
name: ingress
-
nginx
subjects:
-
kind: ServiceAccount
name: ingress
-
nginx
namespace: ingress
-
nginx
-
-
-
# Source: ingress-nginx/templates/controller-service-webhook.yaml
apiVersion: v1
kind: Service
metadata:
labels:
helm.sh
/
chart: ingress
-
nginx
-
4.0
.
1
app.kubernetes.io
/
name: ingress
-
nginx
app.kubernetes.io
/
instance: ingress
-
nginx
app.kubernetes.io
/
version:
1.0
.
0
app.kubernetes.io
/
managed
-
by: Helm
app.kubernetes.io
/
component: controller
name: ingress
-
nginx
-
controller
-
admission
namespace: ingress
-
nginx
spec:
type
: ClusterIP
ports:
-
name: https
-
webhook
port:
443
targetPort: webhook
appProtocol: https
selector:
app.kubernetes.io
/
name: ingress
-
nginx
app.kubernetes.io
/
instance: ingress
-
nginx
app.kubernetes.io
/
component: controller
-
-
-
# Source: ingress-nginx/templates/controller-service.yaml
apiVersion: v1
kind: Service
metadata:
annotations:
service.beta.kubernetes.io
/
exoscale
-
loadbalancer
-
description: NGINX Ingress Controller
load balancer
service.beta.kubernetes.io
/
exoscale
-
loadbalancer
-
name: nginx
-
ingress
-
controller
service.beta.kubernetes.io
/
exoscale
-
loadbalancer
-
service
-
healthcheck
-
interval:
10s
service.beta.kubernetes.io
/
exoscale
-
loadbalancer
-
service
-
healthcheck
-
mode: tcp
service.beta.kubernetes.io
/
exoscale
-
loadbalancer
-
service
-
healthcheck
-
retries:
'1'
service.beta.kubernetes.io
/
exoscale
-
loadbalancer
-
service
-
healthcheck
-
timeout:
3s
service.beta.kubernetes.io
/
exoscale
-
loadbalancer
-
service
-
strategy: source
-
hash
labels:
helm.sh
/
chart: ingress
-
nginx
-
4.0
.
1
app.kubernetes.io
/
name: ingress
-
nginx
app.kubernetes.io
/
instance: ingress
-
nginx
app.kubernetes.io
/
version:
1.0
.
0
app.kubernetes.io
/
managed
-
by: Helm
app.kubernetes.io
/
component: controller
name: ingress
-
nginx
-
controller
namespace: ingress
-
nginx
spec:
type
: LoadBalancer
externalTrafficPolicy: Local
ports:
-
name: http
port:
80
protocol: TCP
targetPort: http
appProtocol: http
-
name: https
port:
443
protocol: TCP
targetPort: https
appProtocol: https
selector:
app.kubernetes.io
/
name: ingress
-
nginx
app.kubernetes.io
/
instance: ingress
-
nginx
app.kubernetes.io
/
component: controller
-
-
-
# Source: ingress-nginx/templates/controller-daemonset.yaml
apiVersion: apps
/
v1
kind: DaemonSet
metadata:
labels:
helm.sh
/
chart: ingress
-
nginx
-
4.0
.
1
app.kubernetes.io
/
name: ingress
-
nginx
app.kubernetes.io
/
instance: ingress
-
nginx
app.kubernetes.io
/
version:
1.0
.
0
app.kubernetes.io
/
managed
-
by: Helm
app.kubernetes.io
/
component: controller
name: ingress
-
nginx
-
controller
namespace: ingress
-
nginx
spec:
selector:
matchLabels:
app.kubernetes.io
/
name: ingress
-
nginx
app.kubernetes.io
/
instance: ingress
-
nginx
app.kubernetes.io
/
component: controller
revisionHistoryLimit:
10
minReadySeconds:
0
template:
metadata:
labels:
app.kubernetes.io
/
name: ingress
-
nginx
app.kubernetes.io
/
instance: ingress
-
nginx
app.kubernetes.io
/
component: controller
spec:
hostNetwork: true
dnsPolicy: ClusterFirst
containers:
-
name: controller
image: serenade11
/
ingress
-
nginx
-
controller:v1.
0.0
imagePullPolicy: IfNotPresent
lifecycle:
preStop:
exec
:
command:
-
/
wait
-
shutdown
args:
-
/
nginx
-
ingress
-
controller
-
-
-
election
-
id
=
ingress
-
controller
-
leader
-
-
-
controller
-
class
=
k8s.io
/
ingress
-
nginx
-
-
-
configmap
=
$(POD_NAMESPACE)
/
ingress
-
nginx
-
controller
-
-
-
validating
-
webhook
=
:
8443
-
-
-
validating
-
webhook
-
certificate
=
/
usr
/
local
/
certificates
/
cert
-
-
-
validating
-
webhook
-
key
=
/
usr
/
local
/
certificates
/
key
securityContext:
capabilities:
drop:
-
ALL
add:
-
NET_BIND_SERVICE
runAsUser:
101
allowPrivilegeEscalation: true
env:
-
name: POD_NAME
valueFrom:
fieldRef:
fieldPath: metadata.name
-
name: POD_NAMESPACE
valueFrom:
fieldRef:
fieldPath: metadata.namespace
-
name: LD_PRELOAD
value:
/
usr
/
local
/
lib
/
libmimalloc.so
livenessProbe:
failureThreshold:
5
httpGet:
path:
/
healthz
port:
10254
scheme: HTTP
initialDelaySeconds:
10
periodSeconds:
10
successThreshold:
1
timeoutSeconds:
1
readinessProbe:
failureThreshold:
3
httpGet:
path:
/
healthz
port:
10254
scheme: HTTP
initialDelaySeconds:
10
periodSeconds:
10
successThreshold:
1
timeoutSeconds:
1
ports:
-
name: http
containerPort:
80
protocol: TCP
-
name: https
containerPort:
443
protocol: TCP
-
name: webhook
containerPort:
8443
protocol: TCP
volumeMounts:
-
name: webhook
-
cert
mountPath:
/
usr
/
local
/
certificates
/
readOnly: true
resources:
requests:
cpu:
100m
memory:
90Mi
nodeSelector:
kubernetes.io
/
os: linux
serviceAccountName: ingress
-
nginx
terminationGracePeriodSeconds:
300
volumes:
-
name: webhook
-
cert
secret:
secretName: ingress
-
nginx
-
admission
-
-
-
# Source: ingress-nginx/templates/controller-ingressclass.yaml
# We don't support namespaced ingressClass yet
# So a ClusterRole and a ClusterRoleBinding is required
apiVersion: networking.k8s.io
/
v1
kind: IngressClass
metadata:
labels:
helm.sh
/
chart: ingress
-
nginx
-
4.0
.
1
app.kubernetes.io
/
name: ingress
-
nginx
app.kubernetes.io
/
instance: ingress
-
nginx
app.kubernetes.io
/
version:
1.0
.
0
app.kubernetes.io
/
managed
-
by: Helm
app.kubernetes.io
/
component: controller
name: nginx
namespace: ingress
-
nginx
spec:
controller: k8s.io
/
ingress
-
nginx
-
-
-
# Source: ingress-nginx/templates/admission-webhooks/validating-webhook.yaml
# before changing this value, check the required kubernetes version
# https://kubernetes.io/docs/reference/access-authn-authz/extensible-admission-controllers/#prerequisites
apiVersion: admissionregistration.k8s.io
/
v1
kind: ValidatingWebhookConfiguration
metadata:
labels:
helm.sh
/
chart: ingress
-
nginx
-
4.0
.
1
app.kubernetes.io
/
name: ingress
-
nginx
app.kubernetes.io
/
instance: ingress
-
nginx
app.kubernetes.io
/
version:
1.0
.
0
app.kubernetes.io
/
managed
-
by: Helm
app.kubernetes.io
/
component: admission
-
webhook
name: ingress
-
nginx
-
admission
webhooks:
-
name: validate.nginx.ingress.kubernetes.io
matchPolicy: Equivalent
rules:
-
apiGroups:
-
networking.k8s.io
apiVersions:
-
v1
operations:
-
CREATE
-
UPDATE
resources:
-
ingresses
failurePolicy: Fail
sideEffects:
None
admissionReviewVersions:
-
v1
clientConfig:
service:
namespace: ingress
-
nginx
name: ingress
-
nginx
-
controller
-
admission
path:
/
networking
/
v1
/
ingresses
-
-
-
# Source: ingress-nginx/templates/admission-webhooks/job-patch/serviceaccount.yaml
apiVersion: v1
kind: ServiceAccount
metadata:
name: ingress
-
nginx
-
admission
namespace: ingress
-
nginx
annotations:
helm.sh
/
hook: pre
-
install,pre
-
upgrade,post
-
install,post
-
upgrade
helm.sh
/
hook
-
delete
-
policy: before
-
hook
-
creation,hook
-
succeeded
labels:
helm.sh
/
chart: ingress
-
nginx
-
4.0
.
1
app.kubernetes.io
/
name: ingress
-
nginx
app.kubernetes.io
/
instance: ingress
-
nginx
app.kubernetes.io
/
version:
1.0
.
0
app.kubernetes.io
/
managed
-
by: Helm
app.kubernetes.io
/
component: admission
-
webhook
-
-
-
# Source: ingress-nginx/templates/admission-webhooks/job-patch/clusterrole.yaml
apiVersion: rbac.authorization.k8s.io
/
v1
kind: ClusterRole
metadata:
name: ingress
-
nginx
-
admission
annotations:
helm.sh
/
hook: pre
-
install,pre
-
upgrade,post
-
install,post
-
upgrade
helm.sh
/
hook
-
delete
-
policy: before
-
hook
-
creation,hook
-
succeeded
labels:
helm.sh
/
chart: ingress
-
nginx
-
4.0
.
1
app.kubernetes.io
/
name: ingress
-
nginx
app.kubernetes.io
/
instance: ingress
-
nginx
app.kubernetes.io
/
version:
1.0
.
0
app.kubernetes.io
/
managed
-
by: Helm
app.kubernetes.io
/
component: admission
-
webhook
rules:
-
apiGroups:
-
admissionregistration.k8s.io
resources:
-
validatingwebhookconfigurations
verbs:
-
get
-
update
-
-
-
# Source: ingress-nginx/templates/admission-webhooks/job-patch/clusterrolebinding.yaml
apiVersion: rbac.authorization.k8s.io
/
v1
kind: ClusterRoleBinding
metadata:
name: ingress
-
nginx
-
admission
annotations:
helm.sh
/
hook: pre
-
install,pre
-
upgrade,post
-
install,post
-
upgrade
helm.sh
/
hook
-
delete
-
policy: before
-
hook
-
creation,hook
-
succeeded
labels:
helm.sh
/
chart: ingress
-
nginx
-
4.0
.
1
app.kubernetes.io
/
name: ingress
-
nginx
app.kubernetes.io
/
instance: ingress
-
nginx
app.kubernetes.io
/
version:
1.0
.
0
app.kubernetes.io
/
managed
-
by: Helm
app.kubernetes.io
/
component: admission
-
webhook
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: ClusterRole
name: ingress
-
nginx
-
admission
subjects:
-
kind: ServiceAccount
name: ingress
-
nginx
-
admission
namespace: ingress
-
nginx
-
-
-
# Source: ingress-nginx/templates/admission-webhooks/job-patch/role.yaml
apiVersion: rbac.authorization.k8s.io
/
v1
kind: Role
metadata:
name: ingress
-
nginx
-
admission
namespace: ingress
-
nginx
annotations:
helm.sh
/
hook: pre
-
install,pre
-
upgrade,post
-
install,post
-
upgrade
helm.sh
/
hook
-
delete
-
policy: before
-
hook
-
creation,hook
-
succeeded
labels:
helm.sh
/
chart: ingress
-
nginx
-
4.0
.
1
app.kubernetes.io
/
name: ingress
-
nginx
app.kubernetes.io
/
instance: ingress
-
nginx
app.kubernetes.io
/
version:
1.0
.
0
app.kubernetes.io
/
managed
-
by: Helm
app.kubernetes.io
/
component: admission
-
webhook
rules:
-
apiGroups:
-
''
resources:
-
secrets
verbs:
-
get
-
create
-
-
-
# Source: ingress-nginx/templates/admission-webhooks/job-patch/rolebinding.yaml
apiVersion: rbac.authorization.k8s.io
/
v1
kind: RoleBinding
metadata:
name: ingress
-
nginx
-
admission
namespace: ingress
-
nginx
annotations:
helm.sh
/
hook: pre
-
install,pre
-
upgrade,post
-
install,post
-
upgrade
helm.sh
/
hook
-
delete
-
policy: before
-
hook
-
creation,hook
-
succeeded
labels:
helm.sh
/
chart: ingress
-
nginx
-
4.0
.
1
app.kubernetes.io
/
name: ingress
-
nginx
app.kubernetes.io
/
instance: ingress
-
nginx
app.kubernetes.io
/
version:
1.0
.
0
app.kubernetes.io
/
managed
-
by: Helm
app.kubernetes.io
/
component: admission
-
webhook
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: Role
name: ingress
-
nginx
-
admission
subjects:
-
kind: ServiceAccount
name: ingress
-
nginx
-
admission
namespace: ingress
-
nginx
-
-
-
# Source: ingress-nginx/templates/admission-webhooks/job-patch/job-createSecret.yaml
apiVersion: batch
/
v1
kind: Job
metadata:
name: ingress
-
nginx
-
admission
-
create
namespace: ingress
-
nginx
annotations:
helm.sh
/
hook: pre
-
install,pre
-
upgrade
helm.sh
/
hook
-
delete
-
policy: before
-
hook
-
creation,hook
-
succeeded
labels:
helm.sh
/
chart: ingress
-
nginx
-
4.0
.
1
app.kubernetes.io
/
name: ingress
-
nginx
app.kubernetes.io
/
instance: ingress
-
nginx
app.kubernetes.io
/
version:
1.0
.
0
app.kubernetes.io
/
managed
-
by: Helm
app.kubernetes.io
/
component: admission
-
webhook
spec:
template:
metadata:
name: ingress
-
nginx
-
admission
-
create
labels:
helm.sh
/
chart: ingress
-
nginx
-
4.0
.
1
app.kubernetes.io
/
name: ingress
-
nginx
app.kubernetes.io
/
instance: ingress
-
nginx
app.kubernetes.io
/
version:
1.0
.
0
app.kubernetes.io
/
managed
-
by: Helm
app.kubernetes.io
/
component: admission
-
webhook
spec:
containers:
-
name: create
image: serenade11
/
kube
-
webhook
-
certgen:v1.
0
imagePullPolicy: IfNotPresent
args:
-
create
-
-
-
host
=
ingress
-
nginx
-
controller
-
admission,ingress
-
nginx
-
controller
-
admission.$(POD_NAMESPACE).svc
-
-
-
namespace
=
$(POD_NAMESPACE)
-
-
-
secret
-
name
=
ingress
-
nginx
-
admission
env:
-
name: POD_NAMESPACE
valueFrom:
fieldRef:
fieldPath: metadata.namespace
restartPolicy: OnFailure
serviceAccountName: ingress
-
nginx
-
admission
nodeSelector:
kubernetes.io
/
os: linux
securityContext:
runAsNonRoot: true
runAsUser:
2000
-
-
-
# Source: ingress-nginx/templates/admission-webhooks/job-patch/job-patchWebhook.yaml
apiVersion: batch
/
v1
kind: Job
metadata:
name: ingress
-
nginx
-
admission
-
patch
namespace: ingress
-
nginx
annotations:
helm.sh
/
hook: post
-
install,post
-
upgrade
helm.sh
/
hook
-
delete
-
policy: before
-
hook
-
creation,hook
-
succeeded
labels:
helm.sh
/
chart: ingress
-
nginx
-
4.0
.
1
app.kubernetes.io
/
name: ingress
-
nginx
app.kubernetes.io
/
instance: ingress
-
nginx
app.kubernetes.io
/
version:
1.0
.
0
app.kubernetes.io
/
managed
-
by: Helm
app.kubernetes.io
/
component: admission
-
webhook
spec:
template:
metadata:
name: ingress
-
nginx
-
admission
-
patch
labels:
helm.sh
/
chart: ingress
-
nginx
-
4.0
.
1
app.kubernetes.io
/
name: ingress
-
nginx
app.kubernetes.io
/
instance: ingress
-
nginx
app.kubernetes.io
/
version:
1.0
.
0
app.kubernetes.io
/
managed
-
by: Helm
app.kubernetes.io
/
component: admission
-
webhook
spec:
containers:
-
name: patch
image: serenade11
/
kube
-
webhook
-
certgen:v1.
0
imagePullPolicy: IfNotPresent
args:
-
patch
-
-
-
webhook
-
name
=
ingress
-
nginx
-
admission
-
-
-
namespace
=
$(POD_NAMESPACE)
-
-
-
patch
-
mutating
=
false
-
-
-
secret
-
name
=
ingress
-
nginx
-
admission
-
-
-
patch
-
failure
-
policy
=
Fail
env:
-
name: POD_NAMESPACE
valueFrom:
fieldRef:
fieldPath: metadata.namespace
restartPolicy: OnFailure
serviceAccountName: ingress
-
nginx
-
admission
nodeSelector:
kubernetes.io
/
os: linux
securityContext:
runAsNonRoot: true
runAsUser:
2000
|
创建deploy.yaml文件然后执行。输出如下
|
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
|
[root@m1
/
]
# kubectl apply -f nginx-ingress-controller.yaml
serviceaccount
/
ingress
-
nginx created
configmap
/
ingress
-
nginx
-
controller created
clusterrole.rbac.authorization.k8s.io
/
ingress
-
nginx created
clusterrolebinding.rbac.authorization.k8s.io
/
ingress
-
nginx created
role.rbac.authorization.k8s.io
/
ingress
-
nginx created
rolebinding.rbac.authorization.k8s.io
/
ingress
-
nginx created
service
/
ingress
-
nginx
-
controller
-
admission created
service
/
ingress
-
nginx
-
controller created
daemonset.apps
/
ingress
-
nginx
-
controller created
ingressclass.networking.k8s.io
/
nginx created
validatingwebhookconfiguration.admissionregistration.k8s.io
/
ingress
-
nginx
-
admission created
serviceaccount
/
ingress
-
nginx
-
admission created
clusterrole.rbac.authorization.k8s.io
/
ingress
-
nginx
-
admission created
clusterrolebinding.rbac.authorization.k8s.io
/
ingress
-
nginx
-
admission created
role.rbac.authorization.k8s.io
/
ingress
-
nginx
-
admission created
rolebinding.rbac.authorization.k8s.io
/
ingress
-
nginx
-
admission created
job.batch
/
ingress
-
nginx
-
admission
-
create created
job.batch
/
ingress
-
nginx
-
admission
-
patch created
|
查看pod,确认pod状态正常
|
1
2
3
4
5
|
[root@m1 yaml]
# kubectl get pods -A | grep ingress
ingress
-
nginx ingress
-
nginx
-
admission
-
create
-
fpwzh
0
/
1
Completed
0
67m
ingress
-
nginx ingress
-
nginx
-
admission
-
patch
-
4scbx
0
/
1
Completed
0
67m
ingress
-
nginx ingress
-
nginx
-
controller
-
9hh7n
1
/
1
Running
0
67m
ingress
-
nginx ingress
-
nginx
-
controller
-
jk646
1
/
1
Running
0
67m
|
实现外部访问
Ingress绑定web-svc,编写规则
|
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
|
apiVersion: networking.k8s.io
/
v1
kind: Ingress
#声明Ingress
metadata:
name: http
-
ingress
#Ingress的名字
spec:
ingressClassName: nginx
#指定Ingress类,
rules:
-
host: k8s.web.com
#指定域名,可选,也可以不写。如声明了域名,则rules适用与该host
http:
paths:
#路径列表
-
pathType: Prefix
#路径类型,分三种ImplementationSpecific,Exact,Prefix
path:
"/"
#路径(“/”表示可匹配所有路径)
backend:
#定义后端服务
service:
name: php
-
fpm
-
nginx
#svc名
port:
number:
80
|
执行Ingress,然后查看刚刚添加的 Ingress 的状态:
|
1
2
3
|
kubectl get ingress http
-
ingress
NAME CLASS HOSTS ADDRESS PORTS AGE
http
-
ingress nginx k8s.web.com
10.10
.
30.202
,
10.10
.
30.203
80
57m
|
说明: 入口控制器和负载平衡器可能需要一两分钟才能分配 IP 地址。 在此之前,通常会看到地址字段的值被设定为
<pending>。
负载均衡
Ingress 控制器启动引导时使用一些适用于所有 Ingress 的负载均衡策略设置,例如负载均衡算法、后端权重方案等。
值得注意的是,尽管健康检查不是通过 Ingress 直接暴露的,在 Kubernetes 中存在并行的概念,比如 , 允许实现相同的目的。
更新 Ingress
要更新现有的 Ingress 以添加新的 Host,可以通过编辑资源来对其进行更新:
|
1
|
kubectl edit ingress test
|
这一命令将打开编辑器,允许以 YAML 格式编辑现有配置。 修改它来增加新的主机:
|
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
|
spec:
rules:
-
host: foo.bar.com
http:
paths:
-
backend:
serviceName: service1
servicePort:
80
path:
/
foo
pathType: Prefix
-
host: bar.baz.com
http:
paths:
-
backend:
serviceName: service2
servicePort:
80
path:
/
foo
pathType: Prefix
..
|
保存更改后,kubectl 将更新 API 服务器中的资源,该资源将告诉 Ingress 控制器重新配置负载均衡器。
更多【学习Kubernetes笔记——暴露站点服务(Ingress)】相关视频教程:www.yxfzedu.com
相关文章推荐
- Pwn-沙箱逃逸之google ctf 2019 Monochromatic writeup - Android安全CTF对抗IOS安全
- 软件逆向-Wibu Codemeter 7.3学习笔记——AxProtector壳初探 - Android安全CTF对抗IOS安全
- 企业安全-学习Kubernetes笔记——暴露站点服务(Ingress) - Android安全CTF对抗IOS安全
- 企业安全-学习Kubernetes笔记——部署数据库站点(MySql) - Android安全CTF对抗IOS安全
- 企业安全-学习Kubernetes笔记——部署web站点环境(PHP+Nginx) - Android安全CTF对抗IOS安全
- 企业安全-学习Kubernetes笔记——安装NFS驱动 - Android安全CTF对抗IOS安全
- 企业安全-学习Kubernetes笔记——kubeadm安装Kubernetes - Android安全CTF对抗IOS安全
- 软件逆向-wibu软授权(四) - Android安全CTF对抗IOS安全
- 软件逆向-使用IDAPython开发复制RVA的插件 - Android安全CTF对抗IOS安全
- 2-wibu软授权(三) - Android安全CTF对抗IOS安全
- 软件逆向-wibu软授权(二) - Android安全CTF对抗IOS安全
- 软件逆向-wibu软授权(一) - Android安全CTF对抗IOS安全
- 软件逆向- PE格式:分析IatHook并实现 - Android安全CTF对抗IOS安全
- Android安全-安卓API自动化安全扫描 - Android安全CTF对抗IOS安全
- 二进制漏洞- Chrome v8 Issue 1307610漏洞及其利用分析 - Android安全CTF对抗IOS安全
- iOS安全-IOS 脱壳入坑经验分享 - Android安全CTF对抗IOS安全
- 二进制漏洞-Windows UAF 漏洞分析CVE-2014-4113 - Android安全CTF对抗IOS安全
- CTF对抗-lua 逆向学习 & RCTF picstore 还原代码块 - Android安全CTF对抗IOS安全
- Android安全-如何修改unity HybridCLR 热更dll - Android安全CTF对抗IOS安全
- 软件逆向-浅谈编译器对代码的优化 - Android安全CTF对抗IOS安全
2):严禁色情、血腥、暴力
3):严禁发布任何形式的广告贴
4):严禁发表关于中国的政治类话题
5):严格遵守中国互联网法律法规
6):有侵权,疑问可发邮件至service@yxfzedu.com
- 智能手机-手机怎么打包?三个方法随心选!
- 智能手机-香港金融科技周VERTU CSO Sophie谈Web3.0的下一个风口 手机虚拟货币移动支付
- 搜索引擎-外贸网站优化常用流程和一些常识
- 电脑-PHP分类信息网站源码系统 电脑+手机+微信端三合一 带完整前后端部署教程
- 智能手机-手机是否能登陆国际腾讯云服务器?
- 智能手机-GD32单片机远程升级下载,手机在线升级下载程序,GD32在线固件下载升级,手机下载程序固件方法
- 华为-漏刻有时百度地图API实战开发(1)华为手机无法使用addEventListener click 的兼容解决方案
- 架构-LoRaWAN物联网架构
- clickhouse-【总结卡】clickhouse数据库常用高级函数
- java-深入理解ClickHouse跳数索引