软件逆向-Wibu Codemeter 7.3学习笔记——Codemeter API调用及通信协议
推荐 原创看完了回个贴呗,你们的关注是我更新的动力
求一个Wibu AxProtector的license,或者是一个能用的AxProtector,后续研究需要
0x00前言
Wibu Codemeter 是一个非常优秀的加密壳,论坛上讨论、研究的较少,只有少数帖子能够参考 , 我斗胆记录一下我的学习历程,望请抛砖引玉,不吝赐教。
PS:因为wibu codemeter一直没有泄露的源码或者pdb,所以我对函数的命名就很玄学,大家多多包涵
0x01样品
Codemeter SDK(Axprotector)7.3
Ap**s
Gas****
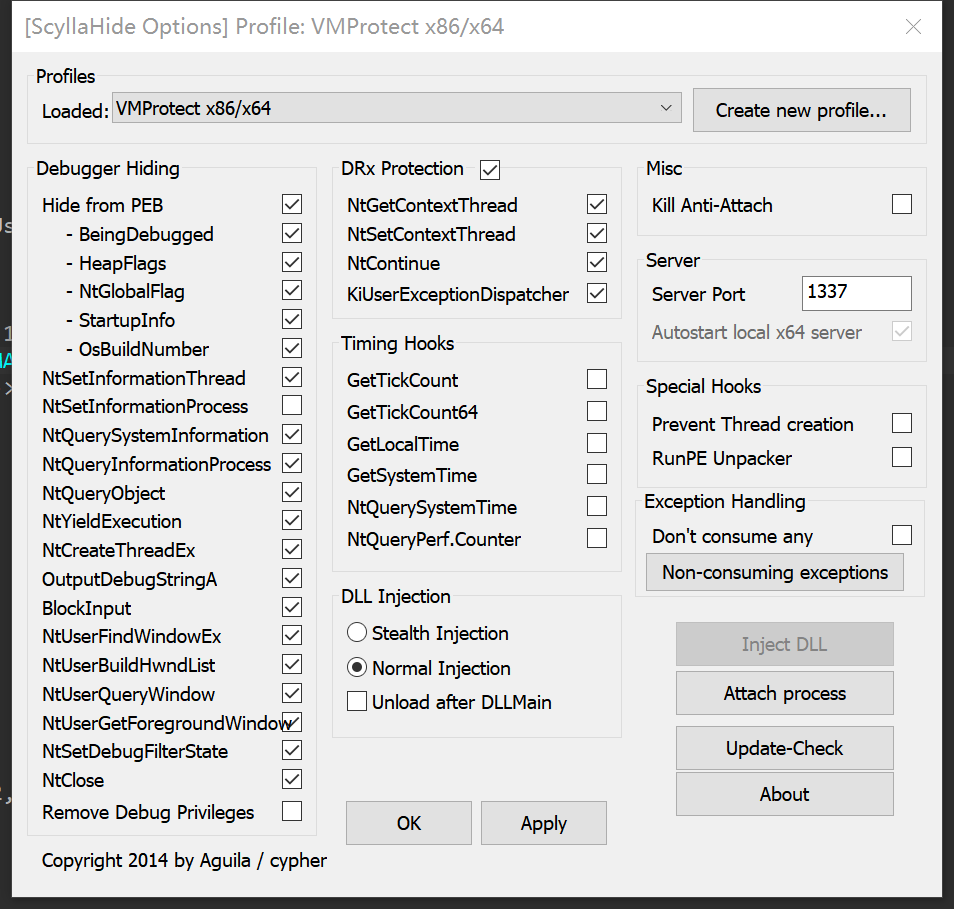
建议使用IDA Pro搭配FindCrypt ScyllaHide,ScyllaHide。ScyllaHide调成下面的选项就能过掉所有的反调试反跟踪手段。
IDA调试前会报一大堆错,直接设置成No Suspend Pass to application静默处理即可,不要试图这时候调试,容易跑飞
EXCEPTION_ILLEGAL_INSTRUCTION No Application Silent
EXCEPTION_ACCESS_VIOLATION No Application Log
EXCEPTION_WX86_BREAKPOINT No Application Log
MS_VC_EXCEPTION No Application Silent
0x02初步分析
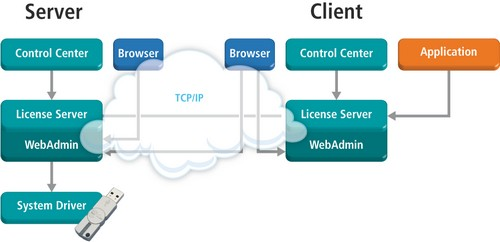
Codemeter整体架构类似flexlm,rlm,都为server-client式的授权系统但破解难度上来说前者是后者的十倍甚至九倍。
Server Codemeter.exe(主要负责CmContainer即license的授权管理,为重点研究对象) CodemeterCC.exe CmWebAdmin.exe(为Codemeter.exe的图形化交互界面不重要)
Client wibucm32.dll wibucm64.dll(负责架起未用AxProtector加密的用户软件与Server间的桥梁,能被aheadlib的方式破掉)
被Axprotector保护的用户软件(直接与Server通信)
对于java,.Net,python则是通过WibuCmNET.dll,CodeMeter.jar等间接调用wibucm32(64).dll,大同小异不再赘述
下面贴一段从Ap**s中扒下来进行授权的代码,Ap**s本体调用wibucm64.dll中的函数来实现授权
if ( a1[8] == 2 )
{
memset(&CMACC, 0, sizeof(CMACC));
CMACC.mflCtrl |= 0x100u;
setReleaseDate(&CMACC, *a1);
CMACC.mulFirmCode = a2;
CMACC.mulProductCode = a1[6] + 9000;
if ( (unsigned int)sub_1813506F0(v7) )
{
CMACC.mulSerialNumber = sub_1813506F0(v8);
CMACC.musBoxMask = sub_1813506D0(v9);
}
strncpy(CMACC.mszServername, "localhost", 0x80ui64);
hcmse = CmAccess2(0i64, &CMACC);//获取对应license的指针,失败,不存在返回0
hcmse_1 = hcmse;
if ( hcmse )//判断一,必修得有这个license
{
v35 = (void ***)hcmse;
len = CmGetInfo(hcmse, 4i64, 0i64); // CM_GEI_ENTRYDATA 0x0004
len_1 = len;
if ( len >= 528 )
{
v18 = len / 0x210ui64;
v19 = (int)v18;
entrydata = (CMENTRYDATA *)operator new(saturated_mul((int)v18, 0x210ui64));
if ( (unsigned int)CmGetInfo(hcmse_1, 4i64, entrydata) )//获取license的用户自定义数据
{
if ( (int)v18 > 0 )
{
secret_data = entrydata->mabData;
do
{
v24 = *((_DWORD *)secret_data - 4);
if ( (_WORD)v24 == 64 && (v24 & 0xFFFF0000) == 0x10000 ) //判断二:用户自建算法
{
v25 = *((_DWORD *)secret_data - 1);
if ( v25 >= 1 )
a1[14] = *secret_data;
if ( v25 >= 2 )
a1[15] = secret_data[1];
if ( v25 >= 3 )
a1[16] = secret_data[2];
if ( v25 >= 4 )
a1[17] = secret_data[3];
if ( v25 >= 5 )
a1[18] = secret_data[4];
}
secret_data += 528;
--v19;
}
while ( v19 );
}
if ( a1[9] == a1[14] && a1[10] == a1[15] && a1[11] == a1[16] && a1[12] == a1[17] && a1[13] == a1[18] )
{
v17 = 0;
}
从这段代码以及wibu官方提供的指南可知,wibu codemeter checkout时只是去服务器上查找是否有对应授权,但在客户端上却不进行检查,有也是软件服务商的自建算法。因此,我们需要重点照顾的对象便是CmAccess和CmGetInfo这两个函数。
0x03向CmAccess进发
WibuCm32(64).dll没有加壳所以分析还是比较快乐的,导出的CmAccess通过几层皮套Api到了真正做事的地方(Codemeter Api中所有函数,类型,结构体等都能在Codemeter/Devkit/include/CodeMeter.h中找到,可以稍微减轻点工作量)
CODEMETER_API HCMSysEntry CMAPIENTRY CmAccess(CMULONG flCtrl, CMACCESS *pcmAcc); CODEMETER_API HCMSysEntry CMAPIENTRY CmAccess2(CMULONG flCtrl, CMACCESS2 *pcmAcc);
int __thiscall cm_access(int calltbl, int flCtrl, CMACCESS2 *cmacc, int isCMACCESS2)
{
int calltbl_1; // esi
UINT_PTR len; // eax
int hcmse; // eax
char isCMACCESS2_1; // cl
unsigned int mulUsedRuntimeVersion; // eax
char flCtrl_1; // di
void *v10; // eax
_DWORD *v11; // eax
_BYTE *v12; // eax
__int16 v13; // ax
char v14; // al
int hcmse_1; // edi
CMACCESS2 *cmacc_2; // eax
int v17; // eax
char v18; // al
unsigned int serverversion; // eax
unsigned int runtimeversion; // [esp+10h] [ebp-188h]
int v22; // [esp+14h] [ebp-184h]
CMACCESS2 *cmacc_1; // [esp+18h] [ebp-180h]
CMACCESS2 *cmacc_3; // [esp+1Ch] [ebp-17Ch]
int buf_1[56]; // [esp+28h] [ebp-170h] BYREF
__int128 v26; // [esp+108h] [ebp-90h] BYREF
unsigned int buf[16]; // [esp+118h] [ebp-80h] BYREF
_QWORD buf_2[6]; // [esp+158h] [ebp-40h] BYREF
int v29; // [esp+194h] [ebp-4h]
calltbl_1 = calltbl; // /*
// flags for mflCtrl in CMACCESS 280000h CM_ACCESS_SUBSYSTEM+
// */
// /* flags for kind of access */
// #define CM_ACCESS_USERLIMIT 0x00000000
// #define CM_ACCESS_NOUSERLIMIT 0x00000100
// #define CM_ACCESS_EXCLUSIVE 0x00000200
// #define CM_ACCESS_STATIONSHARE 0x00000300
// #define CM_ACCESS_CONVENIENT 0x00000400
// /* mask for the access modes */
// #define CM_ACCESS_STRUCTMASK 0x00000700
//
// /* no validation check of the entry data */
// #define CM_ACCESS_FORCE 0x00010000
// /* constant for searching a fitting FSB entry */
// #define CM_ACCESS_CHECK_FSB 0x00020000
// /* constant for searching a fitting CTSB entry */
// #define CM_ACCESS_CHECK_CTSB 0x00040000
// /* allow normal subsystem access if no CmContainer is found */
// #define CM_ACCESS_SUBSYSTEM 0x00080000
// /* force FI access to prevent access to a FC:PC=x:0 */
// #define CM_ACCESS_FIRMITEM 0x00100000
//
// /* flag access to borrow license */
// #define CM_ACCESS_BORROW_ACCESS 0x01000000
// /* flag release to borrow license */
// #define CM_ACCESS_BORROW_RELEASE 0x02000000
// /* flag check borrowed license */
// #define CM_ACCESS_BORROW_VALIDATE 0x04000000
// /* flag ignore entry state for release to borrow license */
// #define CM_ACCESS_BORROW_IGNORESTATE 0x08000000
//
// #define CM_ACCESS_BORROW_MASK 0x0f000000
// /* flag ignore Linger Time of License */
// #define CM_ACCESS_IGNORE_LINGERTIME 0x10000000
cmacc_3 = 0;
cmacc_1 = 0;
len = 0x2C0;
if ( !(_BYTE)isCMACCESS2 )
len = 0xB0;
if ( !sub_385100((void *)calltbl, cmacc, len) )// ->sub_7D17A0 检查输入参数
// 给出的内存地址无效, 错误 113.
return 0;
if ( !cmacc )
{
LABEL_5:
(*(void (__thiscall **)(int, int))(*(_DWORD *)calltbl_1 + 4))(calltbl_1, 105);// 指定了一个无效的参数, 错误 105.
return 0;
}
isCMACCESS2_1 = isCMACCESS2;
if ( (_BYTE)isCMACCESS2 )
{
cmacc_1 = cmacc;
if ( !cmacc->mulFirmCode && cmacc->mulProductCode == 0x186A0 )
cmacc->mflCtrl |= 0x10000u;
if ( cmacc->mulLicenseQuantity > 1 )
{
mulUsedRuntimeVersion = cmacc->mulUsedRuntimeVersion;
if ( mulUsedRuntimeVersion )
{
if ( mulUsedRuntimeVersion < 0x614083E )
goto LABEL_5;
}
else
{
cmacc->mulUsedRuntimeVersion = 0x614083E;
}
}
}
else
{
cmacc_3 = cmacc;
if ( !cmacc->mulFirmCode && cmacc->mulProductCode == 100000 )
cmacc->mflCtrl |= 0x10000u;
}
flCtrl_1 = flCtrl;
if ( flCtrl < 0 )
{
v10 = (void *)sub_383BC0();
if ( !sub_383E90(v10) )
{
(*(void (__thiscall **)(int, int))(*(_DWORD *)calltbl_1 + 4))(calltbl_1, 101);// 未找到CodeMeter服务器, 错误 101.
return 0;
}
isCMACCESS2_1 = isCMACCESS2;
}
v22 = 0;
while ( 1 )
{
if ( isCMACCESS2_1 )
{
hcmse_1 = cmaccesss2((_BYTE *)calltbl_1, flCtrl_1, cmacc_1);// cmaccess2重点
cmacc_2 = cmacc_1;
}
else
{
memset((__m128i *)buf_1, 0, sizeof(buf_1));// cmaccess1
buf_1[1] = -1;
buf_1[2] = 0;
LOBYTE(buf_1[3]) = 0;
buf_1[4] = 0;
buf_1[5] = 0;
buf_1[6] = -1;
buf_1[7] = 0;
LOBYTE(buf_1[8]) = 0;
buf_1[0] = (int)&YS0061::`vftable';
LOBYTE(buf_1[9]) = 10;
memset((__m128i *)&buf_1[10], 0, 0xB8u);
v29 = 0;
v11 = (_DWORD *)sub_32CD60();
cmacc_3->mulReserved1 = getpid(v11);
v12 = (_BYTE *)sub_383BC0();
if ( sub_384C80(v12) )
cmacc_3->mulReserved1 = 0;
buf_1[10] = flCtrl_1 & 0x13 | 0x10000000;
qmemcpy(&buf_1[11], cmacc_3, 0xB0u);
calltbl_1 = calltbl;
v13 = *(_BYTE *)(calltbl + 500) ? *(_WORD *)(calltbl + 498) : (unsigned __int8)sub_3741C0((_BYTE *)calltbl);
HIWORD(buf_1[17]) = v13;
v14 = send_cm_socket_req(calltbl + 24, buf_1, 184, 8u, 1); //重点
v29 = -1;
buf_1[0] = (int)&YS0061::`vftable';
hcmse_1 = v14 ? buf_1[55] : 0;
sub_39E140(buf_1);
cmacc_2 = cmacc_3;
}
runtimeversion = cmacc_2->mulUsedRuntimeVersion;
if ( !hcmse_1 )
break;
if ( (unsigned __int8)sub_3A2480(hcmse_1) )
{
++*(_DWORD *)(calltbl_1 + 104);
break;
}
memset((__m128i *)buf, 0, sizeof(buf));
sub_370CC0((int)buf);
v29 = 1;
v17 = sub_3A25B0(calltbl_1 + 92, hcmse_1);
sub_39E430(buf, (unsigned __int16)hcmse_1, 0x200B, 0x10u, v17);
v18 = send_cm_socket_req(calltbl_1 + 24, buf, 16, 0x1Cu, 0);// cm_get_info
v26 = 0i64;
if ( !v18 || !sub_39E2A0(buf, (unsigned int)&v26) )
{
(*(void (__thiscall **)(int, _DWORD))(*(_DWORD *)calltbl_1 + 4))(calltbl_1, 0);// good
sub_3A2630((unsigned __int16)hcmse_1);
if ( (unsigned __int8)sub_3A2480(hcmse_1) )
{
++*(_DWORD *)(calltbl_1 + 104);
v29 = -1;
buf[0] = (unsigned int)&YS0065::`vftable';
if ( buf[15] )
(**(void (__thiscall ***)(unsigned int, int))buf[15])(buf[15], 1);
sub_39E140(buf);
break;
}
}
memset((__m128i *)buf_2, 0, sizeof(buf_2));
HIDWORD(buf_2[0]) = -1;
LODWORD(buf_2[1]) = 0;
BYTE4(buf_2[1]) = 0;
buf_2[2] = 0i64;
buf_2[3] = 0xFFFFFFFFi64;
LOBYTE(buf_2[4]) = 0;
LODWORD(buf_2[0]) = &YS0060::`vftable';
BYTE4(buf_2[4]) = 11;
LOBYTE(v29) = 2;
buf_2[5] = (unsigned int)hcmse_1;
send_cm_socket_req(calltbl_1 + 24, buf_2, 8, 8u, 0);
LODWORD(buf_2[0]) = &YS0060::`vftable';
sub_39E140(buf_2);
v29 = -1;
buf[0] = (unsigned int)&YS0065::`vftable';
if ( buf[15] )
(**(void (__thiscall ***)(unsigned int, int))buf[15])(buf[15], 1);
sub_39E140(buf);
flCtrl_1 = flCtrl;
isCMACCESS2_1 = isCMACCESS2;
if ( ++v22 >= 5 )
{
(*(void (__thiscall **)(int, int))(*(_DWORD *)calltbl_1 + 4))(calltbl_1, 127);// CodeMeter客户端和服务端的句柄不一致, 错误 127.
return 0;
}
}
hcmse = (unsigned __int16)hcmse_1;
if ( (_WORD)hcmse_1 && runtimeversion )
{
serverversion = get_server_version((void *)calltbl_1, (unsigned __int16)hcmse_1);
if ( serverversion && serverversion >= runtimeversion )
{
return (unsigned __int16)hcmse_1;
}
else
{
(*(void (__thiscall **)(int, _DWORD))(*(_DWORD *)calltbl_1 + 16))(calltbl_1, (unsigned __int16)hcmse_1);// sub_7CDB80
(*(void (__thiscall **)(int, int))(*(_DWORD *)calltbl_1 + 4))(calltbl_1, 0x7D);// 所连接的CodeMeter 服务器版本过旧, 错误 125.
return 0;
}
}
return hcmse;
}
int __thiscall cmaccesss2(_BYTE *this, char flCtrl, CMACCESS2 *CMACC)
{
_DWORD *v4; // eax
_BYTE *v5; // eax
const char *v6; // edx
void *v7; // ecx
int hcmse; // esi
char *v9; // edi
bool v10; // zf
char v11; // al
void *v13[5]; // [esp+10h] [ebp-28h] BYREF
unsigned int v14; // [esp+24h] [ebp-14h]
const char *v15; // [esp+28h] [ebp-10h]
int v16; // [esp+34h] [ebp-4h]
int buf[188]; // [esp+38h] [ebp+0h] BYREF
__int64 v18; // [esp+328h] [ebp+2F0h] BYREF
int v19; // [esp+330h] [ebp+2F8h]
memset((__m128i *)buf, 0, sizeof(buf));
buf[1] = -1;
buf[2] = 0;
LOBYTE(buf[3]) = 0;
buf[4] = 0;
buf[5] = 0;
buf[6] = -1;
buf[7] = 0;
LOBYTE(buf[8]) = 0;
buf[0] = (int)&YS0062::`vftable';
LOBYTE(buf[9]) = 100;
memset((__m128i *)&buf[10], 0, 0x2C8u);
v16 = 0;
v4 = (_DWORD *)sub_4FCD60(); // get proccess
CMACC->mcmCredential.mulPID = getpid(v4);
v5 = (_BYTE *)sub_553BC0();
if ( sub_554C80(v5) ) // 是否为wine模拟器
CMACC->mcmCredential.mulPID = 0;
CMACC->mcmCredential.mbLibType = 1;
CMACC->mcmCredential.mulLibVersion = 0x71E12D4;
setusername(CMACC);
v19 = 0;
v18 = 0i64;
sub_549300((int)&v18);
LOBYTE(v16) = 1;
v6 = sub_4F9BE0(&v18);
v13[4] = 0;
v14 = 15;
LOBYTE(v13[0]) = 0;
v15 = v6 + 1;
allocstring(v13, (unsigned int)v6, strlen(v6));
LOBYTE(v16) = 2;
sub_57B260((int)&CMACC->mcmCredential, (int)v13);
if ( v14 >= 0x10 )
{
v7 = v13[0];
LOBYTE(v16) = 3;
if ( v14 + 1 >= 0x1000 )
{
v7 = (void *)*((_DWORD *)v13[0] - 1);
if ( (unsigned int)(v13[0] - v7 - 4) > 0x1F )
sub_50EA4C();
}
sub_5D3A97(v7);
}
LOBYTE(v16) = 0;
sub_48FC60((void **)&v18);
if ( sub_57B9C0((__m128i *)CMACC->mcmCredential.mszUserDefinedText, 0x80u) )
{
CMACC->mcmBorrowData.mszClientName[127] = 0;
if ( !strlen(CMACC->mcmBorrowData.mszClientName) )
gethostname(CMACC->mcmBorrowData.mszClientName, 127);
v9 = &CMACC->mcmBorrowData.mszClientName[strlen(CMACC->mcmBorrowData.mszClientName) + 1];
memset((__m128i *)(v9 - 1), 0, 128 - (v9 - &CMACC->mcmBorrowData.mszClientName[1]));
v10 = this[500] == 0;
buf[10] = flCtrl & 0x13 | 0x10000000;
qmemcpy(&buf[11], CMACC, 0x2C0u);
if ( v10 )
{
buf[128] = (unsigned __int8)sub_5441C0(this);
HIBYTE(buf[179]) = 0;
}
else
{
v11 = sub_5441C0(this);
buf[128] = *((unsigned __int16 *)this + 249);
HIBYTE(buf[179]) = v11;
}
if ( send_cm_socket_req((int)(this + 24), buf, 712, 8u, 1) )
hcmse = buf[187];
else
hcmse = 0;
}
else
{
(*(void (__thiscall **)(_BYTE *, int))(*(_DWORD *)this + 4))(this, 105);// 指定了一个无效的参数, 错误 105.
hcmse = 0;
}
buf[0] = (int)&YS0062::`vftable';
sub_56E140(buf);
return hcmse;
}
通过分析,可以一眼丁真的分析可以发现整个cm_access函数中基本上都是参数,版本检查,错误处理的鸡毛蒜皮的小事,而cmacc这个重要的参数最终传进了send_cm_socket_req这个函数。
看一眼send_cm_socket_req的交叉引用,发现这个函数跟基本上所有的Cm API有一腿
send_cm_socket_Req cm_get_info_ cm_access_borrow cm_access CmCalculateSignature_1 CmControl_1 cm_get_info_1 CmProgramS_1 CmBoxIoControl_0 CmCalculateSignature_0 CmControl_0 CmCreateLicenseFile_0 CmCreateProductItemOption_0 CmCreateSequence_0 CmEnablingGetChallenge_0 CmEnablingSendResponse_0 CmExecuteRemoteUpdate_0 CmGetAccountInfo_0 CmGetBoxDiagnosticData_0 CmGetBoxes_0 CmGetContainerInfo_0 CmGetFileInfo_0 CmCalculatePioCoreKey_0 CmEnablingGetApplicationContext_0 CmEnablingWriteApplicationKey_0 CmBoxIoControl CmCalculateSignature CmControl CmExtendedDiscControl_0 CmCreateLicenseFile ...(212 Lines Total)
所以基本断定,授权是在服务器codemeter.exe上进行,wibucm32(64)就是个给人打工的小喽喽。
0x04初探send_cm_socket_req
char __thiscall send_cm_socket_req(int this, _DWORD *buf, int final_length, unsigned int len2, char flag)
{
_DWORD *buf_1; // edi
int v7; // eax
int err_4; // eax
int function_table_006F8A58; // eax
char result; // al
int v11; // eax
int v12; // ebx
char err; // cl
int v14; // eax
int err_2; // eax
int v16; // eax
unsigned __int64 v17; // kr10_8
int v18; // eax
int v19; // eax
int v20; // eax
int v21; // eax
int err_3; // [esp+10h] [ebp-38h]
int v23; // [esp+14h] [ebp-34h]
int v24; // [esp+1Ch] [ebp-2Ch]
char err_1; // [esp+23h] [ebp-25h]
int v26[2]; // [esp+24h] [ebp-24h] BYREF
int time1[2]; // [esp+2Ch] [ebp-1Ch] BYREF
LPCRITICAL_SECTION *v28[5]; // [esp+34h] [ebp-14h] BYREF
buf_1 = buf;
v7 = sub_553BC0(); // 多线程相关
err_4 = sub_554DF0(v7, 0); // should ret 1 Codemeter服务器检测 没启动的话挂起服务
err_3 = err_4;
if ( err_4 != 1 )
{
switch ( err_4 )
{
case 0:
case 2:
case 3:
function_table_006F8A58 = get_function_table_006F8A58();
(*(void (__thiscall **)(int, int))(*(_DWORD *)function_table_006F8A58 + 4))(function_table_006F8A58, 101);// 未找到CodeMeter服务器, 错误 101.
result = 0;
break;
case 4:
v11 = get_function_table_006F8A58();
(*(void (__thiscall **)(int, int))(*(_DWORD *)v11 + 4))(v11, 308);// 该数据无法写入安全区, 错误 308.
goto LABEL_5;
default:
LABEL_5:
result = 0;
break;
}
return result;
}
v28[0] = 0;
sub_4FE310(v28, (LPCRITICAL_SECTION *)(this + 60));
v28[4] = 0;
v12 = 0;
v24 = 3;
v23 = 0;
while ( 1 )
{
get_time(time1);
err = send_cm_req_encrypt((struct_this_2 *)this, buf_1, final_length, len2);// should ret 0 加密数据包并发送
err_1 = err;
if ( err && buf_1[2] == 238 ) // CodeMeter 许可服务器启动仍旧在待定中,错误238.
{
sleep(1000u);
v14 = 20;
v24 = 20;
goto LABEL_24; // try again
}
err_2 = *(_DWORD *)(*(_DWORD *)(this + 40) + 12);// getlasterror
if ( err_2 == 309 ) // CodeMeter许可服务器超载, 访问请求已超时,该请求已被拒绝, 错误309.
{
sleep(1000 * (v23 + 1));
v12 = v23;
v24 = 20;
v14 = 20;
goto LABEL_24; // try again
}
if ( err )
{
LABEL_31:
v21 = get_function_table_006F8A58();
(*(void (__thiscall **)(int, _DWORD))(*(_DWORD *)v21 + 4))(v21, *(_DWORD *)(*(_DWORD *)(this + 40) + 12));// cm_set_error
goto LABEL_32;
}
if ( flag && (err_2 == 101 || err_2 == 102) )// 无法将请求发送至其他CodeMeter服务器, 错误 102.
// 未找到CodeMeter服务器, 错误 101.
{
v16 = sub_553BC0();
err_3 = sub_554DF0(v16, 1);
}
get_time(v26);
v17 = v26[1] + 1000000 * (v26[0] - (__int64)time1[0]) - time1[1];
if ( v17 >= 950
* (unsigned __int64)(unsigned int)(*(int (__thiscall **)(_DWORD))(**(_DWORD **)(this + 40) + 96))(*(_DWORD *)(this + 40)) )
break; // 超时检测(网络,反调试)
v12 = v23;
if ( v23 != 2 || *(_DWORD *)(this + 56) != 1 )
{
buf_1 = buf;
LABEL_23:
v14 = v24;
goto LABEL_24;
}
buf_1 = buf;
if ( (*(_BYTE *)(sub_5269C0() + 132) & 2) == 0 )
goto LABEL_23;
*(_DWORD *)(this + 40) = *(_DWORD *)(this + 48);
v14 = v24 + 1;
*(_DWORD *)(this + 56) = 2;
++v24;
LABEL_24:
v23 = ++v12;
if ( v12 >= v14 )
goto LABEL_28;
}
v18 = *(_DWORD *)(this + 40);
if ( !*(_DWORD *)(v18 + 12) )
*(_DWORD *)(v18 + 12) = 100;
LABEL_28:
switch ( err_3 )
{
case 0:
case 1:
goto LABEL_31;
case 2:
case 3:
v19 = get_function_table_006F8A58();
(*(void (__thiscall **)(int, int))(*(_DWORD *)v19 + 4))(v19, 0x65);// 未找到CodeMeter服务器, 错误 101
break;
case 4:
v20 = get_function_table_006F8A58();
(*(void (__thiscall **)(int, int))(*(_DWORD *)v20 + 4))(v20, 0x134);// 该数据无法写入安全区, 错误 308.
break;
default:
break;
}
LABEL_32:
sub_4FE380(v28);
return err_1;
}
通过分析可以发现,send_cm_socket_req并未实现加密、发送数据的逻辑,除去进行连接服务器等不是那么重要的工作,都转交给send_cm_req_encrypt这个函数
0x05CodeMeter has never been cracked……吗?
对用axprotector保护的axprotector.exe进行分析,尽管原始代码已经变得很抽象但是壳本体倒是没有进行混淆或者是虚拟机保护。抱有侥幸心理用bindiff比对一下,嚯,您猜怎么着,那堆CM API绝大部分都有,连咱心心念念的CmAccess,CmGetInfo都在,并且代码上跟wibucm32中的别无二致。还是通过send_cm_socket_req跟服务器唠嗑,自己就等着服务器给个授不授权的信儿然后解密。
再次我斗胆提出一个思路,望诸多大佬指正:
对于Wibu Axprotector,可以避其锋芒,不直接面对那些反调试,反dump的奇技淫巧,可否对壳与服务器,wibucm32(64).dll与服务器间的协议进行逆向,编写出一个虚假的服务器,让壳以为虚假的服务器进行了可信的授权然后运行呢?
类似的思路已经有人实践,TEAM R2R的codemeter waifu通过伪造wibucm32(64).dll攻击类似Ap**s这种通过调用dll进行授权的软件系统,并且这种攻击方式确实有效。
0x06通信协议(天坑)
诸位先贤( ,)已经指出,Codemeter服务器与客户端间通信的私有协议的加密方式:
生成与时间(getTickCount)相关的random key getTickCount->sha1->randomkey
原始报文进行crc32并与原报文进行拓展
对拓展的报文进行AES-128 CBC加密,密钥,iv拆分于randomkey
这篇文章给出了encrypt_telegram这个函数的实现方式,因此为我们减少了很大的工作量。
int __thiscall getRandomkey(struct_this *this, char flag)
{
int time; // edx
int result; // eax
unsigned int v5; // [esp+4h] [ebp-7Ch] BYREF
_DWORD sha1[24]; // [esp+8h] [ebp-78h] BYREF
char sha1res[20]; // [esp+68h] [ebp-18h] BYREF
if ( flag == 1 )
time = GetTimeFromFile(0);
else
time = GetTickCount() / 1000;
this->time = time; //this + 36
sha1[23] = 0;
v5 = 1000 * time / 1009u;
sha1_init(sha1);
sha1_update(sha1, (unsigned int)&v5, 4u);
result = sha1_final((char *)sha1, (int *)sha1res);
this->key = *(_OWORD *)sha1res; //this + 4
this->iv = *(_OWORD *)&sha1res[4]; //this + 20
return result;
}
int __cdecl bitnegation(_DWORD *a1)
{
if ( a1 )
return ~*a1;
else
return -1;
}
__m128i *__cdecl expand_text(int buf, unsigned int *end_pos, char a3)
{
int v3; // ecx
unsigned int v4; // eax
__m128i *result; // eax
if ( buf )
{
if ( end_pos )
{ // ==========================
// | | |
// ==========================
// (end_pos)
//
// =============================
// | ^ --> |
// =============================
// (ep) (ep+39)
// (new_ep)
// ==============================
// | |
// ==============================
// (new_ep)
//
// ==============================
// | |<=^
// ==============================
//
// ===========================
// | |
// ===========================
// 最终使长度变为16的整数倍
v3 = *end_pos;
v4 = (*end_pos + 0x27) & 0xFFFFFFF0;
*end_pos = v4;
return memset((__m128i *)(v3 + buf), a3, v4 - v3);
}
}
return result;
}
char __thiscall encrypt_telegram(struct_this *this, char *buf, unsigned int *end_pos, char flag)
{
int nCrc; // edi
unsigned int len; // esi
unsigned int len_1; // eax
struct_this *this_1; // [esp+10h] [ebp-Ch]
char crc[4]; // [esp+14h] [ebp-8h] BYREF
this_1 = this;
init(crc);
crc32((unsigned int *)crc, buf, *end_pos);
nCrc = bitnegation(crc);
getRandomkey(this, flag);
len = *end_pos;
expand_text((int)buf, end_pos, 0);
len_1 = *end_pos;
*(_DWORD *)&buf[len_1 - 4] = nCrc; // crc
*(_DWORD *)&buf[len_1 - 8] = len; // 原长
return cm_aes_encrypt_cbc(this_1, buf, end_pos, 0);
}
经过确认,这几个核心函数与中分析结果逻辑上相同,故可认为7.30a版本及之前通信协议的加密方法是相同的,可以进行复用
但应该指出的这篇文章只是分析了encrypt_telegram这个函数及其输入参数,并没有细究其中输入的数据与调用的操作之间的联系。我们最后要做到伪造服务端,这种程度是不够的,因此我们应该对send_cm_socket_req send_cm_req_encrypt这两个函数进行分析,并找出其中的内在规律。
(未完待续,不确定再开一贴还是直接往下写)
2022年12月7日更新 4楼
2022年12月24日更新 修改一些代码,增加可读性
更多【Wibu Codemeter 7.3学习笔记——Codemeter API调用及通信协议】相关视频教程:www.yxfzedu.com
相关文章推荐
- 企业安全-学习Kubernetes笔记——kubeadm安装Kubernetes - Android安全CTF对抗IOS安全
- 软件逆向-wibu软授权(四) - Android安全CTF对抗IOS安全
- 软件逆向-使用IDAPython开发复制RVA的插件 - Android安全CTF对抗IOS安全
- 2-wibu软授权(三) - Android安全CTF对抗IOS安全
- 软件逆向-wibu软授权(二) - Android安全CTF对抗IOS安全
- 软件逆向-wibu软授权(一) - Android安全CTF对抗IOS安全
- 软件逆向- PE格式:分析IatHook并实现 - Android安全CTF对抗IOS安全
- Android安全-安卓API自动化安全扫描 - Android安全CTF对抗IOS安全
- 二进制漏洞- Chrome v8 Issue 1307610漏洞及其利用分析 - Android安全CTF对抗IOS安全
- iOS安全-IOS 脱壳入坑经验分享 - Android安全CTF对抗IOS安全
- 二进制漏洞-Windows UAF 漏洞分析CVE-2014-4113 - Android安全CTF对抗IOS安全
- CTF对抗-lua 逆向学习 & RCTF picstore 还原代码块 - Android安全CTF对抗IOS安全
- Android安全-如何修改unity HybridCLR 热更dll - Android安全CTF对抗IOS安全
- 软件逆向-浅谈编译器对代码的优化 - Android安全CTF对抗IOS安全
- 二进制漏洞-年终CLFS漏洞汇总分析 - Android安全CTF对抗IOS安全
- 软件逆向-自动化提取恶意文档中的shellcode - Android安全CTF对抗IOS安全
- 二进制漏洞-铁威马TerraMaster CVE-2022-24990&CVE-2022-24989漏洞分析报告 - Android安全CTF对抗IOS安全
- 4-seccomp-bpf+ptrace实现修改系统调用原理(附demo) - Android安全CTF对抗IOS安全
- 二进制漏洞-Windows内核提权漏洞CVE-2018-8120分析 - Android安全CTF对抗IOS安全
- CTF对抗-Hack-A-Sat 2020预选赛 beckley - Android安全CTF对抗IOS安全
2):严禁色情、血腥、暴力
3):严禁发布任何形式的广告贴
4):严禁发表关于中国的政治类话题
5):严格遵守中国互联网法律法规
6):有侵权,疑问可发邮件至service@yxfzedu.com